The CooperToons Cure
for the
Common Code!
(With a Little About Julius Caesar, Benedict Arnold, Peggy Shippen, George Washington, and Major John André Thrown In)

Simple Ciphers
At some point every kid plays around with "secret messages". If you've read Jean Sheppard's In God We Trust All Others Pay Cash, you remember how Ralphie sent off for a Little Orphan Annie Secret Decoder Ring. And how stunned he was when he found the - quote - "secret message" - unquote - was simply "Be sure to drink your Ovaltine." In other words, a "crummy commercial".
But codes and ciphers - and they are not exactly the same thing - are part of modern life with our plethora of passwords, on-line computer storage, and need for secure communications. And of course in the unending requirements for espionage - both foreign and domestic - coding and encryption has become, we are assured, an integral and necessary part of national security.
But most of all, codes and ciphers have been a major subtopic of recreational mathematics extending back to antiquity. The Mesopotamians, Greeks, Romans, Hebrews, and Arabs all used codes for business and pleasure.
OK. What's the difference between a code and a cipher? Well, a code is the more general and can be anything to obscure the meaning of a message. Usually words or phrases are replaced by apparently unrelated words and phrases.
But a cipher is a one-to-one substitution of the letters of a message with other letters or symbols. However the word "code" is commonly used when we really mean "cipher", we will do the same if it won't confuse things too much.
Keeping It Simple, Julius
Before the advent of computers - which can code and decipher messages quickly - an ideal cipher was one that could be easily encrypted by the sender and read by the recipient with ease. It should also be impossible to "break". That is, no one without the key should be able to figure it out. The definition, though, is somewhat self-contradictory as our examples will show.
OK. Let's consider the following cipher.
Sa daeop pda eya pkiknnks.
This message was created by what is called a simple substitution cipher of the type you read about in the Sherlock Holmes story, "The Adventure of the Dancing Men". Substitution ciphers are - obviously - where a single letter is substituted for something else. These codes are among the oldest and most popular but also the easiest to crack - as Sherlock showed us - simply by looking at letter frequencies and positions and word length.
First, the #1 rule in breaking simple substitutions. The most frequent letter in English is e and which accounts for about 12 % of the letters in a text. That may not seem like a much, but even in fairly short messages, e is likely to appear most often.
And in our coded message above, we see a occurs the most - four times. So you would guess here a is used for e. So we fill in the e's.
-e -e--- --e --e --------.
We now see that two words pda and eya are both three letter words ending in e. There are, of course, many such words. But the most frequently used three letter word - in fact the most commonly used word in English - is the - and it ends in "e".
So which one is "the", if either?
Well, if eya is the, then the sentence can be partly filled in as:
-e -e--- --e the --------.
... which isn't too helpful. It's not necessarily wrong, but just not helpful.
But if we let pda be the, then we can assign p = t and d = h and get:
-e he--t the --e t-------.
... which appears a bit more promising. So we'll pursue this line of attack.
With our new working hypothesis, note that the second word could be heart. If so, then e = a and o = r. So what is a good guess for the first word, then? There are really only three possibilities: Be, We, and Me. None makes any sense with heart.
Then is there another five letter word beginning with he and ending in t?
Here's where a word puzzle reference book comes in handy. Such books - which have now been replaced with online resources - will list words of certain lengths in alphabetical order. And after a brief consultation, we find there are not many other words that fit this description. But there is one candidate worth testing. This is the word heist.
Note, too, there that if the second word is heist, then e = i. Then the first letter of the fourth word must also be i. So filling in the letters gives us:
-e heist the i-e t-------.
Ah, ha! Now We makes sense, and we know that s = w. And we also have the last letter:
We heist the i-e t------w.
For the fourth word, if you run through the alphabet for the second letter, there are two reasonable possibilities: ire and ice. Only the last of these makes sense and is in fact an example of underworld jargon:
We heist the ice t------w.
Finally, what is an eight letter word beginning with t and ending in w? If we consult our word book, there is only one common word that fits the bill. That's tomorrow.
We heist the ice tomorrow.
OK. We have deciphered the message, but have we cracked the code? Nope. Not yet. A single message does not a cracked code make.
To really crack the code, we need to see if we can figure out the substitutions for all other letters. And so we start by listing what we know and what we don't know. This is easy:
| Cipher | = | Translation |
| A | = | ? |
| B | = | ? |
| C | = | Y |
| D | = | ? |
| E | = | A |
| F | = | ? |
| G | = | C |
| H | = | D |
| I | = | E |
| J | = | ? |
| K | = | ? |
| L | = | ? |
| M | = | I |
| N | = | ? |
| O | = | K |
| P | = | ? |
| Q | = | M |
| R | = | N |
| S | = | O |
| T | = | P |
| U | = | ? |
| V | = | ? |
| W | = | S |
| X | = | ? |
| Y | = | ? |
| Z | = | ? |
Now a lot of the time you'll see no pattern and just have to wait for more messages to be intercepted (and cracked). But in this case it only takes minimal reflection to see there is a pattern here. And so we can fill in the blanks pretty easily.
| Cipher | = | Translation |
| A | = | W |
| B | = | X |
| C | = | Y |
| D | = | Z |
| E | = | A |
| F | = | B |
| G | = | C |
| H | = | D |
| I | = | E |
| J | = | F |
| K | = | G |
| L | = | H |
| M | = | I |
| N | = | J |
| O | = | K |
| P | = | L |
| Q | = | M |
| R | = | N |
| S | = | O |
| T | = | P |
| U | = | Q |
| V | = | R |
| W | = | S |
| X | = | T |
| Y | = | U |
| Z | = | V |
In other words, each letter has simply been advanced four places, and where letters spill off at the end, they are simply sent to the beginning. And with this key in hand, if any further messages are intercepted, they can be read.
Such a code is called the Caesar Cipher as Julius was supposed to have used in his military campaigns. These ciphers are sometimes implemented using a double wheel where both have the alphabet and one is nested inside the other. You set the wheels so one letter is over another and use the new letters as indicated.
The Caesar Wheels - among other names - are the same as Ralphie's Little Orphan Annie Decoder Ring. Over the years, a number of toy manufacturers have sold these devices particularly in the days when - quote - "secret clubs" - were popular as marketing gimmicks.
Changing the wheel setting every so often was supposed to help protect the security. But you can also create substitution ciphers where there is no apparent pattern. But even with random switching of the letters, substitution ciphers are easy to break. No spy in his right mind would use a simple substitution code.
So what code, you ask, would a spy in his right mind use?
For that we'll have to review a bit about one of the most important and successful of America's general's in the Revolutionary War. A man whose achievements and military victories helped defeat the British and win America's independence.
No, we don't mean him. We mean Benedict Arnold.
Benedict's Boner: Book Codes
(With an Excursion into a Most Unusual Episode in American History)

Benedict and Peggy
Actually, which code the spies used depended on what resources were available to them. This has changed over the years. But one thing that was available once the spies became officers and gentlemen were books. And with books came the book codes.
As the name implies, a book code is a code where the sender and recipient agree to use a specific book as a key for coding the message. There are a number of book codes, some simpler, some more complex.
The most common book code - and this is an actual code, not a cipher - is where you represent whole words rather than just transpose letters. Of course you need to specify the word's location in an agreed upon manner. Then the recipient - who also has a copy of the book - can take your message and look up the words.
For instance, suppose George Washington - who was a master at espionage - wanted to write the message:
Send new dentures at once!
Exactly what would he do?
Well, first he has to pick out a book. Naturally he wants it to be a book that is fairly common. That way the recipient will also be able to get a copy and it won't look suspicious.
The obvious book would be a dictionary since you'll have all the words you need. Similarly the Bible has served as a key, as it is conveniently divided into chapters and verses and so words can be located easily. But both of these books are the first keys a book code breaker would try.
So instead, George might pick out a copy of Shakespeare's complete works, say a copy of the first folio. Because of the unusual pagination in this edition, you can best determine the word by citing 1) the play in the order listed in the table of contents, 2) the page of the play on which the word appears, 3), the column, 4) the line, and then 5) you count the number of words in the line until you reach the word you want.
With this key and using the first folio, George's message comes out as:
30/4/2/25/4 8/2/1/5/8 dentures 34/1/1/30/1 6/6/1/64/1
In other words, for the first word we pick the 30th play (which is Julius Caesar), the fourth page of the play, the second column, the 25th line, and the fourth word. That happens to be, yes, send. You continue to look up the other words, and you end up with the original message.
Obviously using book codes is tedious and time consuming for both the sender and recipient. You also need to have not just the same book, but the same edition or else there's no guarantee that the words will occur at the same place. And note that if you don't have the word in the book, you have to simply write it in.
A simpler (albeit somewhat less satisfactory) alternative is to create your own key. The words are given their own symbol - usually a number - and everyone has a copy of the key. As with a book code, the recipient looks the word up, and so can read the message.
This was the tack used by George's top spy organization, the Culper Ring organized by Benjamin Tallmadge and who created the code. Copies of the code have survived but because the table is rather lengthy, we've put it on a separate page in a new window which you can see if you click here.
Of course if the enemy ends up with a copy of the key, your secrecy is blown. And it can take a while before you finally realize that the other side is reading your messages. So when it came to pick a code, Benedict Arnold stuck with a straightforward book code.
A lot of Americans know that Benedict was a traitor but they don't always know the details of his treachery (or patriotism if you're British). It's an interesting and amusing story unless you were some of the ones involved.
Early on Benedict was one of the most celebrated heroes of the American Revolution. But after a couple of years he became disgruntled. He had risked his life in battle, been badly wounded at Saratoga (almost losing his leg), and yet for his efforts all he got was an accusation of shady dealings and profiteering when he was military governor of Philadelphia.
Actually Benedict had been working on various schemes to repay his mounting debts. Alas, in doing so he had irritated a lot of his fellow officers and also a number of Congressmen by what they saw as his grasping and greedy ways. But George Washington was sympathetic to who at the time was his favorite general. Although after the investigation into Benedict's finances George felt obliged to issue a mild reprimand, he thought Benedict was a valuable officer and planned to give Benedict a new and important command.
There are some historians who think it was Arnold's young wife, the former Margaret Shippen - called Peggy by her friends and who was 20 years Benedict's junior - who prodded him to switch sides. Now in the more polite biographies Peggy's family is dubbed "neutral" in the revolution. That is, the Shippens expressed no preference for or against independence. This is true enough, but it's also true that when the British occupied Philadelphia, Peggy and her dad were quite friendly with the English soldiers, entertaining the officers in their home, and reciprocating their invitations.
Peggy had become particularly friendly with a British officer, Major John André. John was young (he was thirty), handsome, elegant, and educated. He was also living in Benjamin Franklin's house, and he ripped off a lot of Benjamin's stuff when he left.
John, like most of the British officers, had paid cash for his rank. That was in fact the normal way it was done. Of course, once you paid for your commission - John bought in as a captain - you were theoretically promoted based on seniority and accomplishments. By 1780, John was a major and on the staff of British General Sir Henry Clinton as his Head of Intelligence. That is, John was Sir Henry's chief spy.
If you read about Benedict you may think he switched sides rather abruptly. Maybe, but there is evidence that he had been sending dribs and drabs of information about troop and supply locations to the British for quite a while. Probably he sent the messages via Peggy who had kept up her correspondence with John once the British pulled out of Philadelphia.
In any case, Benedict finally decided to switch sides and to do it in a big way. He made contact with Sir Henry Clinton and asked for enough dough - £20,000 - to clear his debts plus a nice fat pension of a few hundred pounds paid out per year as well as £10,000 to compensate for lost property. He also wanted to have a general's rank and an active command in the British Army. Sir Henry said fine but Benedict had to have something to give.
So Benedict hatched a plan. With his injury from Saratoga he persuaded George that he needed a desk job. But one with military importance - like being the commander of the strategically located fort at West Point on the Hudson River. Benedict offered to let Sir Henry and his troops just waltz in and take over. Then the British would control the traffic on the river and split New England from the rest of the colonies. Sir Henry liked the idea and asked for a specific plan.
Benedict started writing letters to John and he did so in code. He used a book cipher based on two volumes: Commentaries on the Laws of England and An Universal Etymological English Dictionary by Nathan Bailey. The code would identify a word by page, line, and location within the line. Very simple.
Since book ciphers can be recognized as such by anyone with any familiarity with codes, Benedict wrote the messages in invisible ink. And again showing Peggy was definitely in cahoots with her hubby even if not the instigator, the messages were written between the lines of her chatty letters.
An example of the code - we have some of the original letters - is part of a letter written by Benedict to John on the 12th of July 1780:
As 158.9.25 and 115.9.12 are 226.9.3'd by. 236.8.20ing , 131.9.21, 163.9.6 -- it is 177.8.6 that the 156.8.11'z 236.9.28. be 234.9.3ed as well as the .98.8.22s I 128.9.25 up, and a 159.8.5 for 236.8.21's 149.27 'on, and a 255.9.11.-- 13.8.6'd for that 211.8.14 ----- which I have 168.8.20ed, in a 158.8.8, 189.6.17, 10.9.9. This .189.8.17 Sir .300.8.4 290.9.20 7 not, I 31.9.13 think 282.9.12. 152.12.12th.80 --- I am Sir, Your Humble Servant, 12, 1780
Mr. John Anderson 172.9.12 ---- P.S. I have 125.8.15, 61.8.28. in the 30.8.8er, but 30.8.8. S. 300.8.4 will 264.9.26 him with 231.9.27 223.8.1 in 116.8.19 He 14.8.9's the 61.8.28, 196.9.16. in him 189.8.17, 294.9.29, 39.4.24, 48.8.19, 228.8.23 183.8.2. me. The 30.8.8'er .290.9.20 .39.9.24 me |200| 126.9.141s, and .190.8.11 the .220.8.50. to 45.8.10 A----- s, who is 222.9.15ed, to 216.9.22. the 80.8.8 for Mr. 172.9.12 172.9.12
... which means:
As Life and fortune are risked by serving His Majesty, it is Necessary that the latter shall be secured as well as the emoluments I give up, and a compensation for Services agreed on and a Sum advanced for that purpose - which I have mentioned in a letter which accompanies this, which Sir Henry will not, I believe, think unreasonable. I am Sir, your humble Servant. July 12, 1780, [J. Moore].
Mr. Jn Anderson P.S. I have great confidence in the Bearer, but beg Sir Henry will threaten him with his resentment in case he abuses the confidence placed in him, which will bring ruin on me. The Bearer will bring me 200 Guineas, and pay the remainder to Captn A----- who us requested to receive the deposit for Mr. Moore.
This text was translated - or at least copied - by the Loyalist poet, Jonathon Odell. The names "Mr. Moore" and "John Anderson" refer to Benedict and John André respectively. We also have to admit even this brief excerpt gives us an indication of Benedict's rather suspicious and quarrelsome nature. And that he wanted some quick cash.
Originally Benedict wanted the cash upfront. If the plan failed, well, that wasn't his fault. But Sir Henry said no dice. You want the cash, we have to get West Point.
With the new restrictions, Benedict wanted a personal meeting with a British officer to finalize details. John felt that if he was personally involved he'd get a promotion from a lowly (ptui) major to a lieutenant colonel. So they arranged a final meeting at night at the house of Joshua Hett Smith, the son of a local judge. John's visit could be explained as a parley between a British officer and an American general. Such meetings were by no means uncommon. So John passed through the American lines with a flag of truce. But as he spoke with Benedict, the boat waiting in the river for him was fired on by American artillery. So it pulled out leaving John stranded on shore.
Now Benedict and John should have found another boat, and under another flag of truce have John rowed back. The other option to have John spend the night at West Point was out of the question. After all, George was on his way for a visit, and if he sat down to breakfast with Benedict, Peggy, and a British officer, he might wonder just what the heck was going on. So Benedict told John he had to get back to the British lines that night. To smooth things on, Benedict gave John a written pass and a horse.
A fairly recent book tells us that John kept his British uniform on. Unfortunately from John's own letters and those exchanged by George and Sir Henry, there's no doubt that John changed into civilian clothes despite an order from Sir Henry that John was not to carry any incriminating documents and to stay in uniform. That way, if worse came to worse, John would be taken and held simply as a prisoner of war. Officers were usually exchanged pretty quickly, and when captured, were treated fairly well. They normally were - quote - "confined" - unquote - in inns and taverns although they did have to pay the costs themselves.
The story of how John got captured is a bit complex and not all tellings are identical. But it seems all went well until John got to Tarrytown. There he was stopped by three men which the more courteous histories describe as militiamen. Some stories say John thought they were British and identified himself as such. Realizing his faux pax, he then tried to bribe them. Certainly the - quote - "militiamen" - unquote - seemed most interested in seeing if John has some dough on him.
John offered them his gold watch saying that's all he had. But the men couldn't believe a high class dude like John didn't actually have coin of the realm. So they made him undress and in his boot they found the papers. Although only one of the men could read, he recognized fortification plans and realized that they had a spy on their hands. The men took John to a colonial officer, Colonel John Jameson.
Some stories simply say Colonel Jameson placed the Englishman under arrest. Other accounts say that he was confused by the passes and sent John back to Benedict. Then belatedly realizing something was up, he sent the three militiamen to fetch John back. In any case, John did end up as a prisoner of Colonel Jameson.
Colonel Jameson was suspicious of his prisoner, but he did not realize Benedict was the cause of the problem. So he sent a report to Benedict at West Point. He said that they had caught a spy, and he had the plans of West Point on him. However, Benjamin Tallmadge was also told of the capture. Benjamin decided the matter was serious and had the actual documents - which included Benedict's pass - forwarded, not to Benedict, but to George who was also heading to West Point.
When Benedict got Colonel Jameson's message, he nearly dropped a load. Although Colonel Jameson might not have understood the significance of a British officer having a pass approved by Benedict, you could bet your boots George would. After telling Peggy to sit tight, Benedict hopped on a boat and made it to the British lines.
The next morning George showed up, and he expected to see a smiling Benedict and gracious Peggy welcoming him with the hospitality befitting the arrival of their commander-in-chief. But Benedict was nowhere to be found and Peggy was still up in her room. The officers on Benedict's staff seemed confused and some had not been told George was coming.
After breakfast, the messenger sent by Benjamin showed up, and he handed George the documents. If there was ever a time George almost lost his cool this was it. He now realized Benedict was a traitor and to make matters worse, Peggy pretended to go nuts once she learned her husband had skinned out. George, being convinced by her stellar performance (which had Peggy shrieking in hysterics while wearing a most revealing nightgown) sent her to her dad in Philadelphia.
John at first thought he would be simply treated as a prisoner of war, but when he learned he would be charged as a spy, he realized he was in a tight spot. The British had been particularly hard on American spies such as Nathan Hale, who had been a classmate of Benjamin Tallmadge at Yale. Worse (for John), the British tended not to bother with pesky trivialities like trials, and Nathan had been hanged simply on the orders of the British General William Howe. So George was not prepared to be lenient. He did, though, make sure John was tried by a board of fourteen officers. They all agreed John was a spy. So John was sentenced to be hanged.
John's capture brought on a flurry of letters between George and Sir Henry which have survived. George pointed out that the case that John was a spy was pretty much air tight. John had used a flag of truce to disguise a surreptitious military mission - a violation of the laws of war - and had changed into civilian clothes and had assumed a false identity. He had also been captured in American controlled territory carrying intelligence intended for the enemy. What we have is literally the textbook definition of a spy.
Sir Henry's defense for John was what you'd expect when there really is none. He said that John had been in a uniform when he met with Benedict, and Benedict - who Sir Henry pointed out was one of George's own officers - had given John a proper military pass that allowed him free passage.
Sir Henry was really stretching it and he knew it. John himself wrote a letter to Sir Henry that not only absolved Sir Henry of blame but also admitted he had put on civilian clothes and concealed the plans, both actions contrary to Sir Henry's orders. It was about as much a confession as you could have.
Sir Henry offered an exchange. Certainly said George, He'd happily swap John for Benedict. Sir Henry said no, afraid such a trade would discourage other wavering Americans from defecting.
Although Benedict and John met on the banks of the Hudson, they had originally planned to meet at the house of Joshua Smith, the son of a local judge. As Joshua and his family were known to harbor Tory sentiments, he too was arrested and tried as a spy. He claimed he had thought nothing nefarious with General Arnold meeting a British major. Meetings of British and American officers were pretty common, particularly for discussing prisoner exchanges.
But such an explanation is almost certainly bogus. Still Joshua was acquitted for lack of evidence. After the war he went to England, but later when things cooled down he returned to New York. He died there in 1818.
And John? Well, he was hanged October 2, 1780. He's now buried in Westminster Abbey.
Benedict wrote George asking that his clothes be sent to him and that Peggy should be offered all protection. He also protested that what he had done was for the good of his country. He didn't mention anything about £20,000.
On the surface, Benedict's treachery was quite the coup for the British. After all, one of the most famous and able American generals had switched sides. Surely, those bumbling naive colonists would now realize that all was lost and come around.
The truth is Benedict's brouhaha accomplished absolutely nothing. The Americans still held West Point, and with the death of John André the British had lost one of their best intelligence officers. Still the British felt oblidged to give Benedict his general's commission.
Sad to say - for Benedict - his value as a British general was pretty minimal. He managed to evade a kidnapping attempt by George who had arranged for a hefty Sergeant Major John Champe to grab Benedict one night as he went to the latrine. Sergeant Major Champe offered to just kill Benedict but George said no. If they couldn't catch him, then let him go. He wanted Benedict alive to stand trial.
British General Benedict Arnold first fought in Virginia. There he hit is first snag. Remember, Benedict was a mere (ptui) "colonial" who had as a young man actually had to work for a living. So he could never obtaining social parity with the other officers who made their money from a rich family.
Because of his lowly status some of the British officers refused to serve under him. And those that did noted he was particularly interested in military actions that would increase his wealth - that is, that would let him earn "prize money". He was seen by some as grasping and ambitious and at one time he was suspected of poisoning his superior to facilitate promotion.
Having a general no one wanted to serve under put Sir Henry Clinton in a dilemma. So he recalled Benedict. Back in New York, Benedict was a pain in the rear end. He was always telling Sir Henry where to attack (among the suggestions were Philadelphia and West Point). He even got to the point where he sent suggestions to Sir Henry's superiors in London without telling Sir Henry.
Sir Henry finally sent Benedict to attack New London, Connecticut which was not only a base of American Privateers but where Benedict lived when he was running his shipping business. In the end, Benedict burned down most of the town.
Then Benedict attacked Fort Griswold. There he refused to accept an offer of surrender and wiped out almost all of the Americans. So the Americans now not only saw Benedict as a traitor, but as a murderous traitor who would burn down his own hometown.
He wasn't too popular with his English superiors either since in the attack at Fort Griswold the British casualty rate was among the highest of the war. Benedict also found himself having to explain why he had burned down a town he was supposed to capture. The wind, he said, had shifted.
Six weeks after the battle at Fort Griswold, the news arrived that Cornwallis surrendered at Yorktown. Benedict immediately demanded he be put in charge. Then he - a real general - would win the war. Sir Henry decided Benedict's services were no longer required.
Of course, after the war Benedict ended up in England. On the surface he was treated with respect, although the truth was that most of the English saw him less as a noble and patriotic Englishman fighting for King and Country that as a sour, grumpy opportunist whose bumbling resulted in the capture and death of a young and popular officer.
Poor Benedict! He should have stuck with the Americans where he had a real friend in George Washington if no one else. The £30,000 upfront money plus the yearly pension never materialized (after all, the British never got West Point). So Benedict asked Lord Cornwallis (of all people) for a job in the East Indian Company. The request was, of course, promptly refused.
Benedict's next tact was to request compensation from the Americans for the loss of his property and assets - which coincidentally was almost the £30,000 he wanted from the English. Fat chance, and he finally gave up in 1785.
With few prospects in England, Benedict and a girlfriend - Peggy remained in England until 1787 - went to Canada. He began to trade with the West Indies. He did OK, but not great, and once his business activities got him burned in effigy. Seven years later he was back in England.
During the French Revolution England was still at war with France, and Benedict again asked for a command in the English Army. And again the request was turned down. Then he petitioned the government for restitution for his losses during the war. The government said no soap.
So Benedict did what lots of English merchants did. He got a commission as a privateer. That is, he commanded a ship that was licensed to attack French shipping and seize and sell the ships and their cargo. He concentrated his efforts in the West Indies which did a brisk trade with France.
On one of his trips, he sailed into the island of Guadeloupe. Unfortunately, the French had taken over the island, and they immediately took Benedict and his crew prisoner.
Benedict, the French said, was a spy and would be hanged. But then the British set up a blockade around Guadeloupe and possibly with the help of a small bribe, Benedict slipped through a porthole and on a makeshift raft made it to a British ship.
The dramatic escape brought Benedict some (he thought) well-deserved accolades. Alas, it got him neither more money nor an official command, but only another thirteen thousand acres in Canada. Soon afterwards, in 1801, Benedict died and was buried in England where today most people have never heard of him.
Better Communication
We saw that substitution codes are easy to crack and book codes are a pain to use. So almost from the start people tried to figure how to write ciphers where you break up the ability to analyze the code for letter frequency and word length. And this requirement led to the creation of polyalphabetic codes.
A simple way to create a polyalphabetic code - which of course are ciphers - is simply to use the Caesar cipher wheel but advance the wheel in the course of writing a single message. Of course, everyone has to know the rules of the advancement but polyalphabetic systems were major improvements in creating secure codes.
But what if you didn't have or lost your Caesar Wheel? Well, you could create the following table. This was something everyone could make for themselves as long as they had pencil and paper.
| A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
| B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A |
| C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B |
| D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C |
| E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D |
| F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E |
| G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F |
| H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G |
| I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H |
| J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I |
| K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J |
| L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K |
| M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L |
| N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M |
| O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N |
| P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O |
| Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P |
| R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q |
| S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R |
| T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S |
| U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T |
| V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U |
| W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V |
| X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W |
| Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X |
| Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Z |
To create a polyalphabetic code you would begin on some pre-arranged row. Say it was Row #5. You find the letter in the row you need and then move up to the top of the column. Say you want to encrypt the word SEND, we see that on Row #5 that "S" corresonds to Column "O".
Now the manner you change rows is up to you. Let's do it every letter and simply move down one row. So in "Send" the next letter to encrypt would use Row #6. In that case, "E" is "Z". We then advance to Row #7 where "N" is "H" and finally we end up on Row #8 where "D" is "W". So "SEND" would be written "OZHW".
But suppose later in the message you have the word "send" again. It would be only coincidence if you are at Row #5. It might be Row #10. In that case "S" is "J", and advancing a row with each letter, we end up encoding "SEND" as "JUCR".
So we see that in one message the same word is coded in two different ways. Someone who thought he was cracking a simple substitution cipher would be stuck.
Many polyalphabetic codes have their own names. Among them are the Alberti, Autokey, Vigenère, Beaufort, Porta, Running Key, Gronsfeld, and probably the most famous polyalphabetic cipher, the Enigma Code.
A Mystery Wrapped in an Enigma.

They cracked the code.
The problem is once automatic calculating machines began to show up, the polyalphabetic codes began to get cracked. That's because the frequency, although obscured, is not eliminated. What was needed was a way to more efficiently scramble the alphabet. And in the 20th century the advances in electronoics began to enter into the fields of codes and ciphers.
The most famous of the polyalphabetic ciphers is the Enigma Code used by the Germans in World War II. These messages were encrypted using a combined mechanical/electronic typewriter that would pick a letter from a key and send a signal to a wheel which had the alphabet around the edge. The wheel rotated so it's letter aligned with another wheel so the original letter would be changed to another. But each time a key was pressed, the wheels rotated again so the next time the letter appeared it would be coded to a new letter. You also had multiple wheels in the machine and a single letter would be altered a number of times on a single key press. So patterns and frequencies are disrupted. The Enigma Code was extremely difficult to crack even with a computer.
Which is what the English had. The Enigma Code was broken early in the war and the messages of the German High Command were read in Bletchley Park. The messages were being read so quickly that the Germans became convinced that there was a spy at their headquarters.
You will read on the Fount of All Knowledge that the key to cracking the Enimga Code was when a Polish mathematician constructed a wooden model of what he remembered of the machine. The model allowed the British military intelligence to recgonize what it was and understand the principle of its operation. This story is correct.
But what isn't known very well today - and wasn't at the time - is that the Germans - and this is no joke - had actually filed for a number of patents for their machine. Like most companies they filed in many countries and the British could have simply gone to their patent office and pulled out a copy of the patents and found a complete description of the Enigma device. Sometimes you can't see your hand for your palm.
The Perfect Code
Naturally we have to ask:
Is there any code that is completely unbreakable? Not just practically but also theoretically?
Well, actually yes. In fact, the following cipher:
uzdfmqsdfuqflrrmhxluujv
... has a message most relevant today and is a friendly greeting to our cousins across the sea - our friends with whom George Washington had his minor dispute. The code, though, is completely and entirely unbreakable.
But how, you ask querulously, can we know that?
Because this code was generated by what is called a one-time-pad. The name comes from the day when the key to the cipher was literally printed on a pad of paper. Each sheet was used for only one message and then thrown away. Hence the name.
The pad was a list of random numbers, the numbers varying on the number of characters you used. For instance, the pad could have numbers ranging from 0 to 26 which corresponded to the letter of the alphabet and a blank space.
The point was that only two people - the sender and the recipient - had identical pads with that particular sequence of numbers. Other people could have pads but the numbers would be different.
To use the one-time-pad you would, of course, write down the message. Then you would transcribe the message to the alphabetic location of each letter. That is 0 = space, 1 = A, B = 2, C = 3, ..., Z = 26. Some codes omit spaces altogether
Next you added the numbers from your message to the numbers on the pad. If the sum is greater or equal to 27, you subtract 26. You now have a new sequence of numbers which range from 0 to 26. You write down the letters that correspond to the numbers. You send this as your message.
Suppose the message is intercepted. Well, what they have is a random list of letters with no pattern to either the letter frequencies or word length. That's because adding a series of non-random numbers to a set of random numbers produces random numbers.
As an example of one-time encryption, let's say we have as a one-time-pad:
| 19 | 14 | 2 | 17 | 19 | 19 | 21 | 5 | 12 | 23 | 25 | 16 |
| 2 | 1 | 24 | 25 | 25 | 20 | 1 | 20 | 23 | 9 | 9 | 11 |
| 23 | 9 | 24 | 23 | 17 | 2 | 15 | 25 | 20 | 17 | 17 | 12 |
| 12 | 25 | 19 | 7 | 24 | 11 | 2 | 3 | 0 | 0 | 20 | 1 |
| 14 | 13 | 14 | 25 | 19 | 6 | 4 | 11 | 22 | 0 | 5 | 8 |
| 5 | 22 | 21 | 6 | 13 | 5 | 15 | 24 | 25 | 14 | 11 | 11 |
| 7 | 13 | 24 | 10 | 0 | 7 | 21 | 1 | 23 | 18 | 26 | 18 |
| 10 | 1 | 11 | 21 | 15 | 3 | 12 | 8 | 10 | 2 | 4 | 26 |
| 13 | 24 | 15 | 16 | 9 | 25 | 11 | 14 | 16 | 17 | 3 | 1 |
| 13 | 2 | 6 | 19 | 3 | 22 | 12 | 1 | 0 | 26 | 5 | 14 |
| 22 | 1 | 24 | 15 | 16 | 14 | 6 | 12 | 3 | 26 | 7 | 7 |
| 8 | 4 | 25 | 6 | 19 | 15 | 26 | 1 | 14 | 23 | 24 | 15 |
| 16 | 1 | 2 | 6 | 8 | 21 | 5 | 0 | 9 | 10 | 23 | 6 |
| 7 | 8 | 9 | 23 | 20 | 5 | 24 | 9 | 11 | 16 | 1 | 20 |
| 18 | 3 | 23 | 12 | 5 | 15 | 12 | 24 | 12 | 3 | 12 | 17 |
| 0 | 20 | 9 | 10 | 12 | 15 | 18 | 14 | 19 | 17 | 5 | 9 |
| 12 | 24 | 19 | 11 | 1 | 17 | 2 | 15 | 23 | 1 | 10 | 2 |
| 13 | 10 | 10 | 6 | 22 | 9 | 18 | 5 | 26 | 6 | 8 | 2 |
| 21 | 17 | 8 | 21 | 21 | 12 | 12 | 9 | 13 | 20 | 17 | 26 |
| 19 | 20 | 21 | 14 | 17 | 7 | 11 | 25 | 18 | 24 | 4 | 9 |
| 0 | 22 | 24 | 17 | 14 | 3 | 14 | 21 | 21 | 11 | 3 | 15 |
| 15 | 5 | 21 | 4 | 13 | 23 | 6 | 1 | 19 | 14 | 17 | 2 |
| 26 | 17 | 21 | 6 | 12 | 2 | 16 | 20 | 14 | 1 | 17 | 21 |
| 25 | 19 | 6 | 22 | 0 | 13 | 17 | 1 | 14 | 20 | 19 | 22 |
| 9 | 25 | 23 | 24 | 0 | 18 | 14 | 9 | 1 | 22 | 23 | 18 |
| 26 | 13 | 20 | 2 | 26 | 19 | 21 | 16 | 10 | 25 | 16 | 25 |
| 5 | 10 | 14 | 23 | 26 | 16 | 1 | 17 | 16 | 8 | 3 | 7 |
| 4 | 25 | 5 | 7 | 23 | 12 | 19 | 5 | 13 | 24 | 24 | 0 |
And using this one-time-pad, we would like to know how to encipher "Sweet Fanny Adams".
I thought you would as Captain Mephisto said to Sidney Brand. It's really quite simple as this table shows:
| Message: | S | w | e | e | t | F | a | n | n | y | A | d | a | m | s | ||
| Alphabet Location: | 19 | 23 | 5 | 5 | 20 | 0 | 6 | 1 | 14 | 14 | 25 | 0 | 1 | 4 | 1 | 13 | 19 |
| One-Time-Pad: | 19 | 14 | 2 | 17 | 19 | 19 | 21 | 5 | 12 | 23 | 25 | 16 | 2 | 1 | 24 | 25 | 25 |
| Sum: | 38 | 37 | 7 | 22 | 39 | 19 | 27 | 6 | 26 | 37 | 50 | 16 | 3 | 5 | 25 | 38 | 44 |
| Adjusted Sum* | 12 | 11 | 7 | 22 | 13 | 19 | 1 | 6 | 26 | 11 | 24 | 16 | 3 | 5 | 25 | 12 | 18 |
| Coded Message: | l | k | g | v | m | r | a | f | z | k | x | p | c | e | y | l | r |
* If Sum > 27, subtract 26.
So the message we send is:
lkgvmrafzkxpceylr
And to decipher the message?
Remember the recipient has an identical pad with the same random sequence. He takes the letters, writes down the number of the alphabet for the letter, but now he subtracts the numbers from the one-time-pad. If the resulting difference is less than zero, you add 26. You have now recovered the original alphabet locations.
We see eins mehr that decipherment is easy:
| Cipher: | l | k | g | v | m | r | a | f | z | k | x | p | c | e | y | l | r |
| Alphabet Location | 12 | 11 | 7 | 22 | 13 | 19 | 1 | 6 | 26 | 11 | 24 | 16 | 3 | 5 | 25 | 12 | 18 |
| One-Time-Pad: | 19 | 14 | 2 | 17 | 19 | 19 | 21 | 5 | 12 | 23 | 25 | 16 | 2 | 1 | 24 | 25 | 25 |
| Difference: | -7 | -3 | 5 | 5 | -6 | 0 | -20 | 1 | -12 | 14 | -1 | 0 | 1 | 4 | 1 | -13 | -7 |
| Adjusted Difference*: | 19 | 23 | 5 | 5 | 20 | 0 | 6 | 1 | 14 | 14 | 25 | 0 | 1 | 4 | 1 | 13 | 19 |
| Message: | S | w | e | e | t | F | a | n | n | y | A | d | a | m | s |
* If Difference < 0, add 26.
And hey, presto! We've got the message!
Now there are One-Time-Skeptics that question whether these codes are unbreakable. With today's supercomputers, you can try - to misquote Carl Sagan - billions and billions - of random sequences. In fact with only 2,153,693,963,075,557,766,310,747 possible combinations for this message a computer can try them all and simply eliminate the gibberish answers. Then we pick out the correct answer.
Nicht wahr?
Weeeeeeeeeellllllll, not quite.
Not only is doing billions and billions of searches something that takes a long time even for big computers, but there's a reason why such an approach will never work. True, you'll get a lot of gibberish answers you can throw out. But you'll also get a lot of answers that are not gibberish - but aren't the real answer either.
Ha? (To quote Shakespeare.) How is that possible?
Well, consider this. At some point the computer will generate the following random sequence:
| 15 | 6 | 7 | 21 | 19 | 25 | 26 | 3 | 15 | 11 | 23 | 22 | 3 | 1 | 24 | 15 | 4 |
And look what "message" we get if we plug it in as the one-time-pad.
| Cipher: | l | k | g | v | m | r | a | f | z | k | x | p | c | e | y | l | r |
| Alphabet Location | 12 | 11 | 7 | 22 | 13 | 19 | 1 | 6 | 26 | 11 | 24 | 16 | 3 | 5 | 25 | 12 | 18 |
| One-Time-Pad: | 15 | 6 | 7 | 21 | 19 | 25 | 26 | 3 | 15 | 11 | 23 | 22 | 3 | 1 | 24 | 15 | 4 |
| Difference: | -3 | 5 | 0 | 1 | -6 | -6 | -25 | 3 | 11 | 0 | 1 | -6 | 0 | 4 | 1 | -3 | 14 |
| Adjusted Difference*: | 23 | 5 | 0 | 1 | 20 | 20 | 1 | 3 | 11 | 0 | 1 | 20 | 0 | 4 | 1 | 23 | 14 |
| Message: | w | e | a | t | t | a | c | k | a | t | d | a | w | n |
* If Sum < 0, add 26.
And we have a completely coherent message that makes sense - even more sense than the true message. In fact every and all possible coherent sentences of the same length will be generated by the computer looking at all possible random sequences. And you'll have no idea which was the real message.
But hold on, say the computer savvy. Random numbers generated by computers are not truly random. They are produced by formulas and if you can figure out the formula, then you can reproduce the sequence. That is, random numbers we see today are pseudo-random, not really random.
Well, sometimes. But the one-time-pad sequence we used for our encryption here are not pseudo-random numbers. They are true random numbers and were generated by counting atmospheric electromagnetic noise. These numbers cannot be reproduced by any formula no matter how complex.
Interestingly enough, this ability to generate coherent yet spurious messages by looking for patterns that are really random is the principle behind so many of the famous - quote - "codes" - unquote - where ancient writings - quote - "predict the future" - unquote. You can read about one of the most famous of such - quote - "codes" - unquote - if you just click here.
The one-time-pad, although having perfect security against decryption, has obvious disadvantages. First, both sender and recipient have to have copies of a pad that no one else has. You also have to make sure you don't get the pages out of sequence and above all else, you can't lose the pad.
Electronic versions of the one-time-pad have similar disadvantages. If the sender and receiver have the random key sent to them, then it can be intercepted by someone else. If you can transfer the key securely, then why not just send the message?
An Honorable Profession
The strangest thing about codes and ciphers is that although they have been used by all nations for espionage and good chunks of our national budgets go to spying on countries - including their own - spies themselves have never been treated in a particularly forgiving manner. We saw that John André was shown no quarter even though George Washington himself admitted John's fault was more one of bad luck than criminal intentions. Matters have gotten no more genteel in modern times. The Ottoman Empire in World War I would execute courriers as young as twelve, and as late as World War II, even the United States executed spies who were only sixteen years old.
For this reason, spies go to great lengths not to look like spies and the secret message not to look like secret messages. We mentioned that messages were sometimes written in invisible ink, but this tactic has its drawback since invisible ink - if made visible - is again proof you are spying.
Instead, it helps to make secret messages look like ordinary documents. That can be fairly easy to do, particularly if your "cover" is something that would require using numbers. For instance, if you were a schoolmaster doing spy duty, you could translate a message into numbers and make it look like it was a lesson plan. The degree of encryption might not have to be too complex.
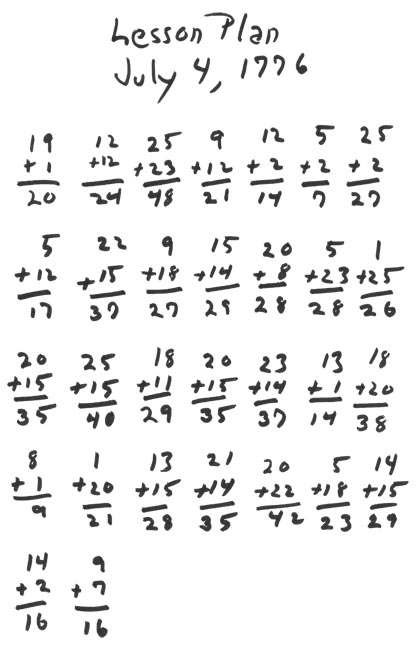
In this case, the only numbers that matter are the top two and the sum is simply a red-herring. The recipient would take the numbers and transpose them back to letters to read the message.
See if you can figure out the message. It's really very simple.
Businessmen spies could also conceal the messages in phony account and ledger books, receipts, or spending records. But the most important key for success in the spy business is not to trust anyone and confide in no one. Some of George's best spies were so secret that their neighbors thought they were Tories even after the war. To this day the names of some of George's spies are a mystery.
The CooperToons Cure
The Cure
The author and illustrator of CooperToons - and other people who have dabbled in codes and ciphers - can offer some cures for these common codes. One - which is kind of slick - is based on a one time pad. That's where you have a message that seems to be a perfectly innocuous and intelligible message and yet this - quote - "message" - unquote - is in fact the encrypted message.
How, you ask, is this possible?
Well, suppose you want to send the message:
Georgie - Drop by today - Sally.
... and you want to disguise this as the message:
Tell Mom I called to say "Hi!"
What you have to do is calculate what one-time-pad you need to change the first message to the second. So we simply back calculate as we did for decoding a message.
| Desired Coded Message | t | e | l | l | m | o | m | i | c | a | l | l | e | d | t | o | s | a | y | h | i | ||||||
| Letter Location | 20 | 5 | 12 | 12 | 0 | 13 | 15 | 13 | 0 | 9 | 0 | 3 | 1 | 12 | 12 | 5 | 4 | 0 | 20 | 15 | 0 | 19 | 1 | 25 | 0 | 8 | 9 |
| Original Message | g | e | o | r | g | i | e | d | r | o | p | b | y | t | o | d | a | y | s | a | l | l | y | ||||
| Letter Location | 7 | 5 | 15 | 18 | 7 | 9 | 5 | 0 | 4 | 18 | 15 | 16 | 0 | 2 | 25 | 0 | 20 | 15 | 4 | 1 | 25 | 0 | 19 | 1 | 12 | 12 | 25 |
| Difference | 13 | 0 | -3 | -6 | -7 | 4 | 10 | 13 | -4 | -9 | -15 | -13 | 1 | 10 | -13 | 5 | -16 | -15 | 16 | 14 | -25 | 19 | -18 | 24 | -12 | -4 | -16 |
| Adjusted Difference* | 13 | 0 | 23 | 20 | 19 | 4 | 10 | 13 | 22 | 17 | 11 | 13 | 1 | 10 | 13 | 5 | 10 | 11 | 16 | 14 | 1 | 19 | 8 | 24 | 14 | 22 | 10 |
| Key | m | w | t | s | d | j | m | v | q | k | m | a | j | m | e | j | k | p | n | a | s | h | x | n | v | j |
* If Difference < 0, add 26.
So - again ignoring punctuation and capitalization - the key would have to be:
m wtsdjmvqkmajmejkpnashxnvj
And we see you can recover the original message if you have the key:
| Key | m | w | t | s | d | j | m | v | q | k | m | a | j | m | e | j | k | p | n | a | s | h | x | n | v | j | |
| Letter Location | 13 | 0 | 23 | 20 | 19 | 4 | 10 | 13 | 22 | 17 | 11 | 13 | 1 | 10 | 13 | 5 | 10 | 11 | 16 | 14 | 1 | 19 | 8 | 24 | 14 | 22 | 10 |
| Coded Message | t | e | l | l | m | o | m | i | c | a | l | l | e | d | t | o | s | a | y | h | i | ||||||
| Letter Location | 20 | 5 | 12 | 12 | 0 | 13 | 15 | 13 | 0 | 9 | 0 | 3 | 1 | 12 | 12 | 5 | 4 | 0 | 20 | 15 | 0 | 19 | 1 | 25 | 0 | 8 | 9 |
| Adjusted Difference* | 7 | 5 | 15 | 18 | 7 | 9 | 5 | 0 | 4 | 18 | 15 | 16 | 0 | 2 | 25 | 0 | 20 | 15 | 4 | 1 | 25 | 0 | 19 | 1 | 12 | 12 | 25 |
| Original Message | g | e | o | r | g | i | e | d | r | o | p | b | y | t | o | d | a | y | s | a | l | l | y |
* If Difference < 0, add 26.
In this case, you send the one-time key either simultaneously or at least near enough in time so the message can be read when needed. Then the key can be destroyed.
But you can see the dilemma. If you can deliver the one-time keys securely and secretly, then you can probably deliver the original messages securely and secretly as well. So why bother?
Well, there are ways to conceal the key. For instance, you can send it as an acrostic. Consider the message:
Martin says that we will try to sparge extra draft kegs, just with more size variety.
Quickly assemble kegs next Monday night and we just now might be equaling what Jerry and Kitty achieved.
Put in newly purified additives and set the hops and xylose isomerase next to Vinny and Jerry's bench.
Tell Mom I called to say "Hi!"
This message does two things:
First, it hides the key quite effectively. With the exception of the last line, the first letter of every other word of the sentences gives you the key (the extra space between words indicates a blank space).
Next, the last line is the coded message itself. That is in a single communication we have both the code and the enciphered message.
But note that if the message was intercepted it can be explained as coming from a tavern keeper and brewer to a partner who was probably a family member as well. And since the acrostic - the key - is simply a gibberish collection of letters, it wouldn't be recognized as either a cipher key or a message.
Still, even for short messages, this encryption method can be quite tedious. And if the method was somehow leaked or obtained by counter espionage, then the secrecy would be lost.
But there is another approach which can be used which is certainly better than encrypting by the most commonly used codes. So we give another example of yes, the CooperToons Cure for the Common Code.
The CooperToons Code has advantages, but of course we can't give exact details or the code would no longer be secret. But the discerning reader can figure out the principles as it is much like using a one-time-pad combined with the principles of polyalphabetic codes. And honesty compels us to say the method is by no means original. Nevertheless, CooperToons believes the message which he has the honor to deliver will never be broken.
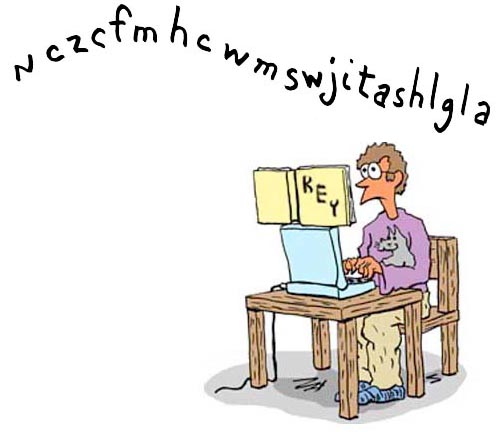
And yes, the message conveyed is the same as the one from the one-time-pad given above (not "Sweet Fanny Adams" but the other one). Using the new CooperToons Cipher the message is rendered:
nczcfmhcwmswjitashlgqla
CooperToons emphasizes that the key is not very complex and everyone either has the key or can easily obtain it. Furthermore automatic coding and decryption can be implemented in virtually any spreadsheet.
And indeed if you know the key, then the message can be easily decoded using the online javascript application which opens in another window if you click here. (You can also download the application as an Excel spreadsheet - which does not require Visual Basic - if you click here.)
We repeat. You have to have the key. But it ain't the one given in the spreadsheet. And in all honesty it involves an aspect of cryptology that, although not difficult, has not been explicitly discussed in this brief essay.
The coding we used for this message is, in fact, the next level of creating a cipher. You can learn about it in many books or webpages about making ciphers. As a hint there are two ways of performing the encipherment and you end up getting the same coded message.
And the key for translating the message is created from a very simple and common - nay, ubiquitous - source. And if the readers saw the answer, they would probably say, "Oy, vey! Why didn't I think of that?
And for those who are interested in creating codes where the encoded message is a perfectly comprehensible but unrelated sentence as we demonstrated above, you can use these applications - either the online or Excel version. Exactly how to do this is, as the mathematics textbooks say, is left as an exercise for the reader.
And in closing, CooperToons will simply say he will be happy to hear if anyone believes they have figured out the key and deciphered the messages in this essay. If a decrypted message is correct, it will be acknowedged as such. So in closing:
Lwihqmxwozumvjxqzve!
References
Introduction to Cryptography: Principles and Applications, Hans Delfs, Helmut Knebl, Springer, 2002.
In God We Trust All Others Pay Cash, Jean Shepherd, Doubleday, 1965
George Washington, Spymaster: How the Americans Outspied the British and Won the Revolutionary War, Thomas Allen, National Geographic Children's Books, 2004
"Spying and Espionage", George Washington's Mount Vernon, http://www.mountvernon.org/george-washington/the-revolutionary-war/spying-and-espionage/
"Benedict Arnold", Biography, http://www.biography.com/people/benedict-arnold-9189320#later-life-and-legacy.
"Why Benedict Arnold Turned Traitor Against the American Revolution", Nathaniel Philbrick, Smithsonian Magazine,
"July 12, 1780 - Benedict Arnold to John André"Spy Letter of the American Revolution From the Collections of the Clements Library, http://clements.umich.edu/exhibits/online/spies/letter-1780july12-code.html
"Correspondence: George Washington and Henry Clinton", http://founders.archives.gov/search/Correspondent%3A%22Arnold%2C%20Benedict%22%20Correspondent%3A%22Washington%2C%20George%22, Foundrers Online, http://founders.archives.gov/, National Archives, http://www.archives.gov/
"Treason is but trusted like the fox: Whatever Happened to Benedict Arnold?", Colonial Williamsburg, https://www.history.org/foundation/journal/Summer01/BenedictArnold.cfm.
"London Ghosts, the Burial Spot of Benedict Arnold", Michale Milne, Changes in Longitude. http://www.changesinlongitude.com/burial-location-of-benedict-arnold-in-london/. A most interesting article showing us the - quote - "crypt" - unquote where Benedict and Peggy are buried. They, with their daughter Sophia, were buried in the basement of the church of St. Mary's of Battersea. Today the room is large and spacious and quite cheerful - in fact, it's the church's kindergarten room with the marker for the Arnolds next a goldfish tank surrounded the kids' art.
Strictly speaking, the marker is likely not the exact final abode of Benedict, Peggy, and Sophia. A priest at the church told a visitor that in 1900 the Thames had flooded and the water got into the crypt. There the bones of the people had been mixed and exactly who is residing where is not a matter of specific record.
More ironically - to Americans - is that the church has a stained glass window - quite nicely done and in good taste - dedicated to Benedict. The only - quote - "monument" to Benedict in the United States is a tribute to his valor at Saratoga. But it doesn't mention Benedict by name.
Jonathan Odell, Loyalist Poet of the American Revolution, Cynthia Edelberg, Duke University Press, 1987.
RANDOM.ORG, https://www.random.org/